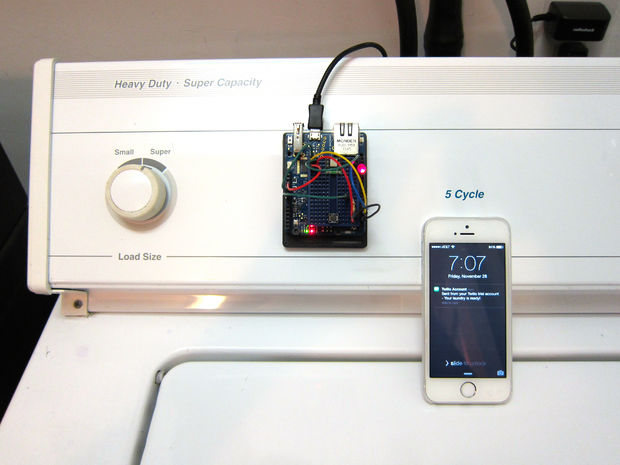
Sick of losing valuable drying time when you forget to take the washing out of the machine? This project allows you to turn your washing machine into an Internet of Things (IoT) device which notifies you via Twitter and sms when the washing is finished. Rather than modifying your washing machine, the project cleverly uses an accelerometer to detect when the washing machine is in use. The project can be made very cheaply from commonly available parts and could be easily finished in a few hours.

Completing this project will teach you a lot about building internet connected devices and could end up saving you a lot of time. To get started check out the instructable from MakerBee.
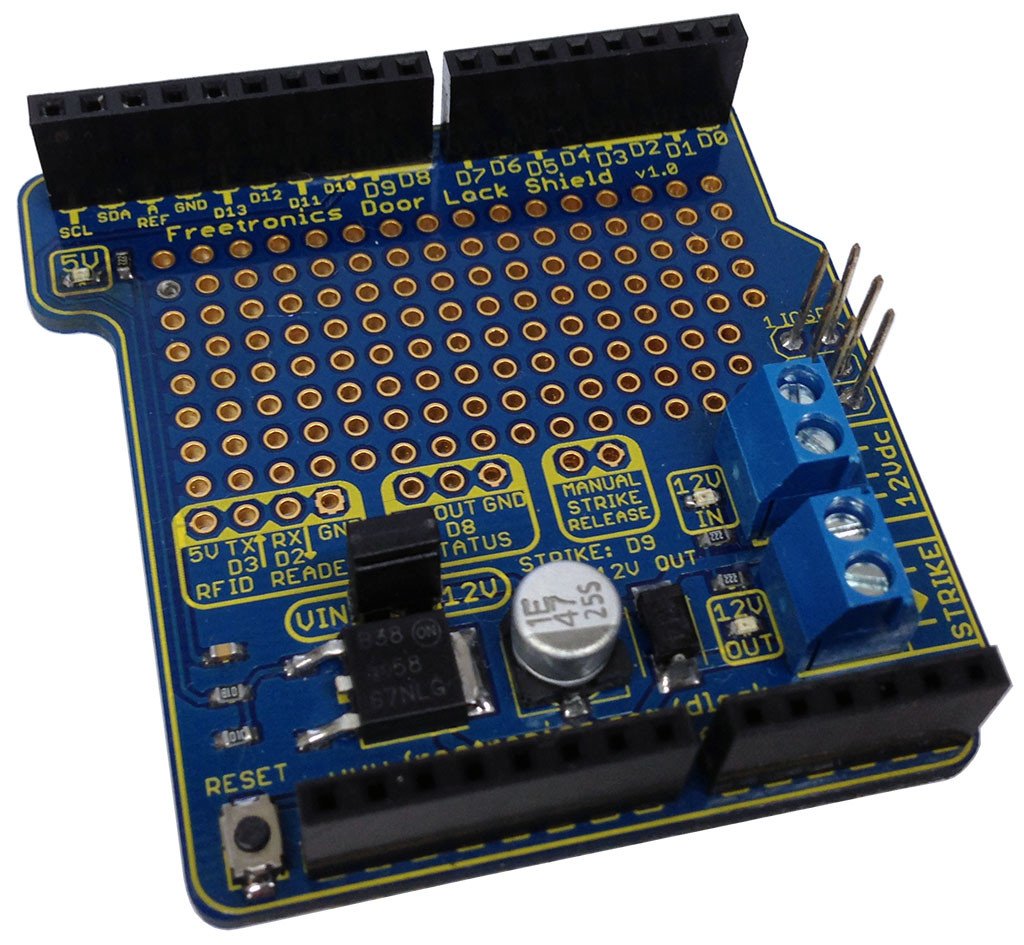
If you are looking for a accelerometer to complete this project, SuperHouse Automation recomends the Freetronics 3-Axis Accelerometer Module. The module has independent X,Y and Z axis outputs ready to connect directly into an Arduino. To find out more and to order check out the product page.
Subscribe to SuperHouse Automation on YouTube to learn more about creating internet of things devices!
Considering optimizing your washing machine? The team at SuperHouse Automation would love to hear how your project goes! Let us know in the comments section below or on Facebook and Twitter.